Cybersecurity, Artificial intelligence
How AI Agents Are Transforming Alert Triage in Security Operations Centers

Author
Vooban
Enterprise SOCs are fighting alert fatigue: too much noise, too many false positives, and too little time. AI agents transform triage by enriching signals, correlating context, and escalating in minutes so teams expand coverage and focus on real threats.
Security Operations Centers (SOCs) face an impossible equation. Enterprise SOCs receive up to 3,000 alerts daily, but a team of analysts can only investigate hundreds of them. The result: 40-62% of alerts go completely ignored, creating dangerous security gaps where real threats hide in the noise.
Traditional SOAR platforms promised to improve alert triage but fall short with their rigid playbook approach. When alerts don't fit predefined criteria, automation fails and escalates to humans, defeating the purpose. It is necessary but insufficient for ambiguous triage.
AI agents represent a fundamental shift in alert triage. These autonomous systems investigate, reason, and decide like human analysts but at machine speed, transforming triage from manual investigation to intelligent automation.
The Alert Fatigue Crisis
Analysts spend 27% of their time chasing false positives during alert triage. A single alert investigation consumes 30-70 minutes. This creates an impossible situation where critical threats slip through while teams chase benign anomalies.
Alert flooding isn’t just volume, it’s noise. Most systems trigger on isolated signals and disconnected data, producing large numbers of false positives that pile up faster than teams can clear them.
This is because traditional systems lack context during triage. A login from a new country triggers an alert without knowing the user is on approved business travel. These "siloed" decisions generate massive false positive rates, eroding trust and wasting time on investigations that lead nowhere.
The math doesn't work: you can't triage 3,000 alerts with a team sized for 100.
AI Agents: Autonomous Investigation at Scale
AI agents function as digital teammates during alert triage, capable of reasoning and adaptive decision-making. Unlike SOAR platforms with rigid playbooks, AI agents are systems that use trained models (often LLMs) alongside tools, data integrations, and guardrails to interpret context and run multi-step analysis without constant human direction.
When a suspicious login triggers an alert, a supervisor AI agent doesn't simply check thresholds during triage, but decomposes the problem into parallel evidence-gathering tasks and assigns them to specialist agents: one autonomously queries IP reputation databases, one examines user travel history, one checks device consistency, and one correlates behavior against baselines. This enrichment happens in parallel across multiple data sources with simultaneous queries, while humans must sequentially log in to different tools to collect and correlate the same information. The supervisor reconciles conflicts, asks follow-up questions only where uncertainty remains, and outputs an auditable triage decision with confidence and next actions.
A real differentiator in alert triage is reasoning capability. If an initial check proves inconclusive, the agent determines what additional data might help and pivots to examine different log sources, mirroring how experienced analysts work through ambiguous triage situations.
Consider a triage scenario: A 3 AM login from an unfamiliar IP triggers an alert. The agent queries the IP (hotel chain), checks the user's calendar (business trip), verifies the device fingerprint (known laptop), and examines VPN logs (no concurrent connections). Within two minutes, it determines this is legitimate and autonomously closes the alert. Triage is complete, accurate, and instant, and the human analyst is not burdened by a false positive.
Starting with a Single AI Agent: A Practical Entry Point
Organizations don't need a full multi-agent architecture to improve alert triage on day one. Starting with a single AI agent focused on high-volume alert types provides a practical entry point that builds confidence while delivering immediate triage efficiency.
This approach offers lower complexity. Many deployments of single AI agents begin targeting suspicious login attempts where they can make a measurable triage impact.
The triage workflow: The agent ingests alerts, enriches them with context, applies behavioral analysis, provides recommendations with confidence scores, and either escalates threats or auto-closes benign alerts. This eliminates the manual investigation that previously consumed analyst time.
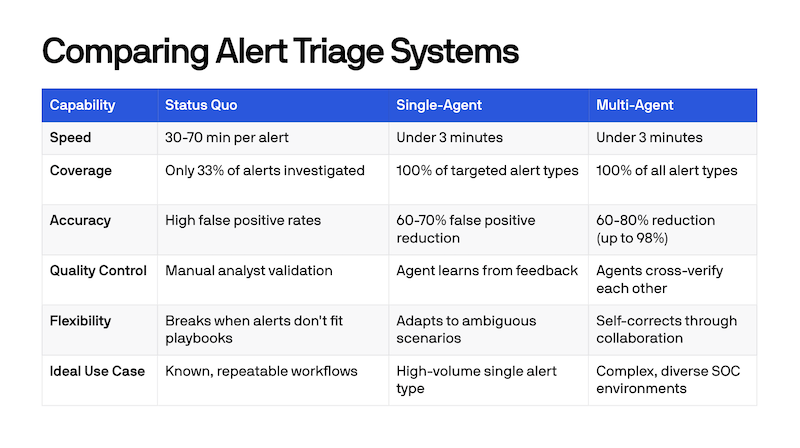
Single-agent triage results typically include a 60-80% false positive reduction, investigation times under three minutes, and 100% coverage for targeted alert categories. Every alert receives consistent triage treatment, ensuring nothing critical is missed due to alert fatigue.
While single-agent workflows deliver value quickly, there are limits to their effectiveness, including no cross-verification to catch triage errors and potential struggles with zero-day attacks. For a robust and cross-referencing agentic defense infrastructure, the evolution should bring you to multi-agent systems as your organization’s AI readiness matures.
Multi-agent Systems: Precision Through Collaboration
Multi-agent architectures amplify triage precision through specialization. Rather than one generalist model, multi-agent systems assign distinct roles: Triage Agent for severity classification, Investigation Agent for threat intelligence, Operation Agent for infrastructure data, Case Management Agent for summarization, and Supervisor Agent for coordination.
The power for alert triage emerges through collaboration. Agents can cross-verify triage findings, engage in adversarial debate, and use consensus mechanisms before final determinations. If one agent flags a file as malicious during triage but another identifies it as a known business tool, the system reconciles facts before escalating.
Advanced triage workflows in security operations often include self-correction loops. When an agent retrieves insufficient data, the system automatically rewrites queries or asks peer agents for second opinions, improving triage accuracy while maintaining speed. As more security platforms adopt the Model Context Protocol (MCP), AI agents can also share context and invoke the same tools through a standardized interface during an investigation.
Even if you deploy a multi-agent system, guardrails and supervision remain essential, with human-in-the-loop workflows ensuring analysts stay in control.
Real-World Results: Metrics That Matter
AI agent triage systems deliver measurable improvements in how SOCs handle alert triage and volume.
The transformation extends beyond metrics. Security teams shift from chasing endless alert notifications to proactive threat hunting and strategic initiatives. Analysts stop spending days gathering context during initial triage and focus on investigating sophisticated attacks, improving detection rules, and addressing security debt.
With AI agents providing 100% alert triage coverage, nothing falls through the cracks due to alert fatigue. The SOC becomes more effective at triage not by working harder, but through intelligent automation.
Strategic Advantages: Beyond Speed and Accuracy
AI agents deliver two critical advantages that transform alert triage beyond just faster investigations.
Complete Attack Stories
AI agents automatically correlate fragmented alerts into unified attack narratives during triage. A single attack generating separate alerts for phishing, malware download, system modification, and network connection gets assembled into one coherent incident timeline. Instead of reviewing raw logs, analysts receive complete "case files" explaining what happened, why it matters, and what systems were affected.
This saves analysts time and effort. Time, because all the information is presented in one source with all the required correlations and analysis. Effort, because rather than tool switching and cross-referencing multiple alerts that seem unrelated, analysts can immediately assess the complete attack chain and determine the appropriate response. Both single-agent and multi-agent systems can correlate related alerts, though multi-agent architectures achieve higher accuracy through cross-verification of their correlations.
Continuous Learning
AI agents refine triage accuracy over time by incorporating feedback. When analysts mark escalated alerts as false positives, agents adjust future triage decisions. They establish behavioral baselines, learning that finance teams access large datasets at month end, developers download tools triggering malware signatures, and executives travel on specific schedules.
When one agent learns a new threat pattern, it shares this insight across the ecosystem. The entire multi-agent triage system benefits without manual updates, maintaining effectiveness as the threat landscape evolves.
The Path Forward
According to Gartner, 40% of enterprise applications will include AI agents by 2026. In security operations, adoption will accelerate as organizations recognize that human analysts alone cannot handle the alert triage volumes and complexity of modern threat landscapes.
Organizations deploying agentic triage today gain immediate advantages: dramatically reduced false positives, investigation times measured in minutes rather than hours, comprehensive alert coverage, and analysts freed from endless manual triage to focus on strategic security work.
As multi-agent architectures are deployed across security teams, they'll expand beyond initial alert triage into automated response, proactive threat hunting, and continuous security posture improvement. The organizations investing in AI-powered alert triage now will define what the future SOC looks like, one where machines handle the scale and humans handle the strategy.
If you want to go further, the CISO Cyber Agentic AI Playbook picks up from here: a practical, step-by-step approach to deploying agents safely across your cybersecurity operations.